
ISO 27001 • ISO 42001 • CMMC • SOC 2 • NIST • Cyber Essentials • DCC
ISO 27001 • ISO 42001 • CMMC • SOC 2 • NIST • Cyber Essentials • DCC
ISO 27001 • ISO 42001 • CMMC • SOC 2 • NIST • Cyber Essentials • DCC
ISO 27001 • ISO 42001 • CMMC • SOC 2 • NIST • Cyber Essentials • DCC
ISO 27001 • ISO 42001 • CMMC • SOC 2 • NIST • Cyber Essentials • DCC
ISO 27001 • ISO 42001 • CMMC • SOC 2 • NIST • Cyber Essentials • DCC
CMMC: Where Compliance Gets Tested — and Most Organisations Fail
CMMC isn’t just another certification to tick off — it’s becoming the line between staying in the defence supply chain and being pushed out of it. Most organisations already have policies, controls, and documentation in place, but that’s not what’s being tested anymore. What matters now is whether those controls actually work, whether the evidence holds up when challenged, and whether your scope makes sense under real scrutiny. That’s where things start to break. CMMC forces a shift from looking compliant on paper to being able to prove, clearly and confidently, that your security stands up in practice — and for many, that’s the difference between winning work and losing it.
CMMC — What It Actually Means
CMMC isn’t just a framework — it’s a structured way of proving whether your organisation can actually protect sensitive defence information under real conditions.
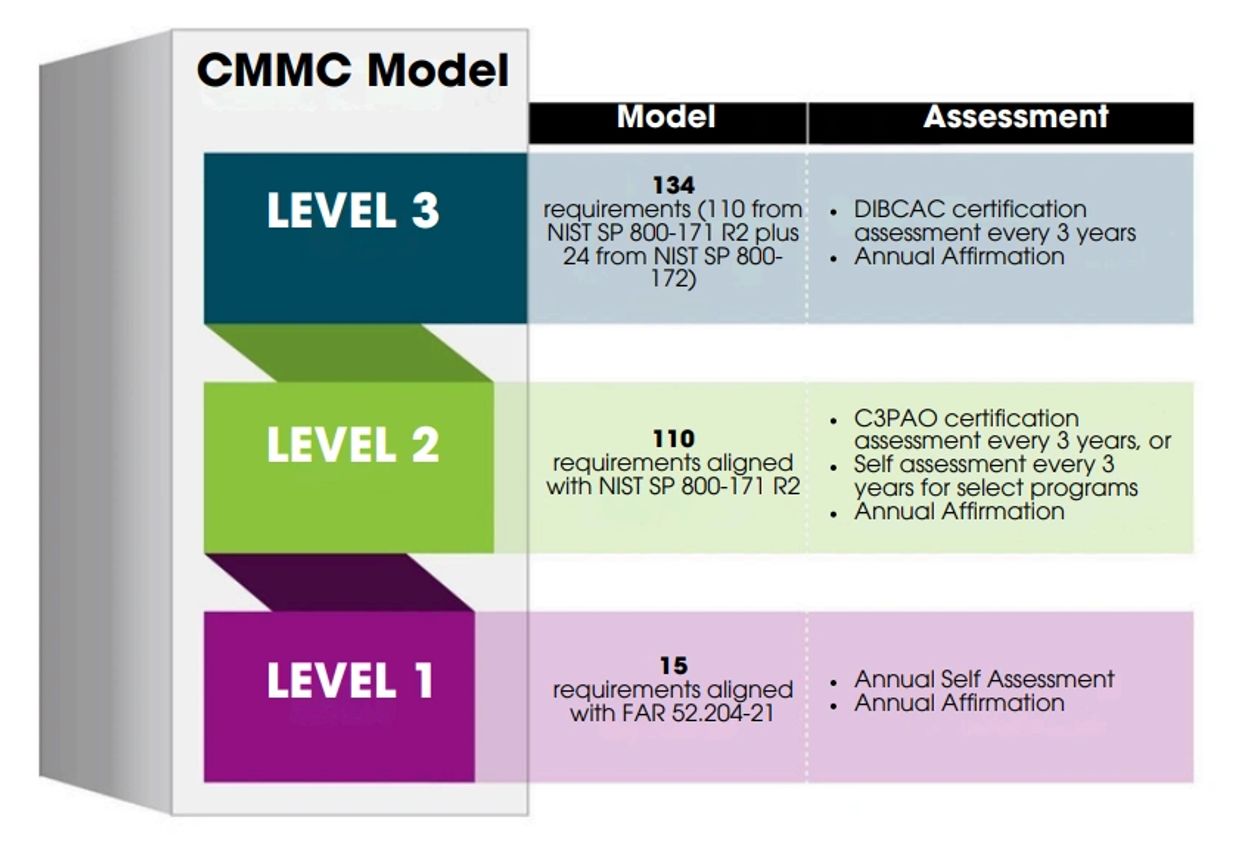
The model is built around defined domains and over 110 security practices, but the levels themselves tell the real story.
At Level 1, organisations are expected to demonstrate basic cyber hygiene — things like controlling access and protecting Federal Contract Information (FCI). It’s the foundation, but it’s not where the real challenge begins.
At Level 2, everything changes. This is where organisations must show that security is not just implemented, but managed and embedded. It aligns directly to NIST 800-171 and focuses on protecting Controlled Unclassified Information (CUI). This is where most organisations start to struggle — not because controls don’t exist, but because they don’t operate consistently or stand up under scrutiny.
At Level 3, the expectation moves further again. Organisations must demonstrate mature, optimised processes capable of detecting and responding to advanced threats. This isn’t about having controls — it’s about proving resilience against real-world attack behaviour.
Across all levels, certification is not self-declared. It is assessed by an independent third party, and that assessment tests more than documentation — it tests whether your environment actually works the way you claim it does.
Governance — Where Most Organisations Break
CMMC governance isn’t about writing policies and assigning ownership on paper. It’s about whether your organisation can consistently operate, maintain, and prove its security posture over time.
In practice, this means:
- Defining clear policies and procedures that reflect how the organisation actually operates
- Assigning responsibility in a way that is visible, understood, and accountable
- Training people so security isn’t theoretical — it’s part of day-to-day behaviour
- Implementing controls that work in real environments, not just in documentation
- Continuously assessing performance to identify where things are breaking
- Engaging independent assessors when ready — and being prepared for challenge
- Fixing gaps properly, not just closing them on paper
- Maintaining evidence that is clear, consistent, and defensible
This is where most organisations fail.
Not because they don’t have policies.
Not because they don’t have tools.
But because what they have doesn’t hold up when tested.
The Bottom Line
CMMC is not about achieving a level.
It’s about proving that your organisation can operate securely under scrutiny — and continue to do so over time.
That’s the difference between:
- looking compliant
- and being trusted in the defence supply chain
Why Most Organisations Fail

Controls exist. They don’t hold up.
Policies and controls may be in place, but they often fail when tested properly.

Evidence exists. It isn’t defensible.
Documents are there, but they are incomplete, inconsistent, or weak.

Used in high-risk environments
Focused on what actually matters
Focused on what actually matters
Built for organisations that cannot afford weak assurance

Focused on what actually matters
Focused on what actually matters
Focused on what actually matters
Working controls, clear scope, and defensible evidence
Not Just Claimed — Proven
John T.
Nilesh R.
Nilesh R.
As a company we have carried many ISO frameworks and had no need for a consultant to support. CMMC on the other hand was a different cattle of fish! The lads and ladies at Blackkyte have been incredible. As a company we had to work to a strict deadline, the team took all the stress away. True professionals and it all honesty are now members of the team to support us as we move forward.
Thank you for you continued support
Nilesh R.
Nilesh R.
Nilesh R.
What an incredible group of consultants. From the minute we engaged they answered the phone and we instantly got a quote. They are all serving and ex serving military professionals, and without them we didn't stand a chance!
Highly recommend and they are flexible to work on all time zones to work alongside our worldwide offices.
KyteAssure

KyteAssure
KyteAssure is the assurance platform built for organisations that need more than compliance — they need systems that withstand audit.
It brings together implementation, maintenance, and audit readiness across ISO 27001, ISO 42001, CMMC, Cyber Essentials, Cyber Essentials Plus, and DCC into one operational environment.
No spreadsheets. No guesswork. No last-minute panic.
What KyteAssure Does
- Centralises your ISMS / AIMS / compliance framework
One platform. Full visibility across all standards. - Tracks real control effectiveness — not just documentation
Know what actually works when tested. - Builds and maintains audit-ready evidence
Structured, traceable, defensible. - Monitors compliance in real time
Live status, gaps, and readiness at a glance. - Prepares you for external assessment
So when the auditor arrives — nothing breaks.

Why It’s Different
Most platforms help you look compliant.
KyteAssure makes you defensible.
It’s built by lead auditors and operational security specialists who know exactly:
what gets tested
where organisations fail
and what “audit-ready” actually means
The Outcome
✔ Controls that operate as intended
✔ Evidence that stands up to scrutiny
✔ Clear, defensible system boundaries
✔ Confidence walking into any audit
Built for Reality
Whether you’re targeting ISO certification, CMMC compliance, or government frameworks, KyteAssure ensures your system isn’t just implemented — it’s proven.
The operating system for audit-ready security
News & Insights
Subscribe
Copyright © 2025 Black Kyte 17 - All Rights Reserved.